System Information & Event Management
Security Operations for the Modern Enterprise
All Data is Secure Data

Extending Security Analysis Beyond IT
- Unified security view of IT and Business applications
- Real-time threat detection and forensics
- Perform analytics and visualization for historical data

Delivering Disruptive Economic Value
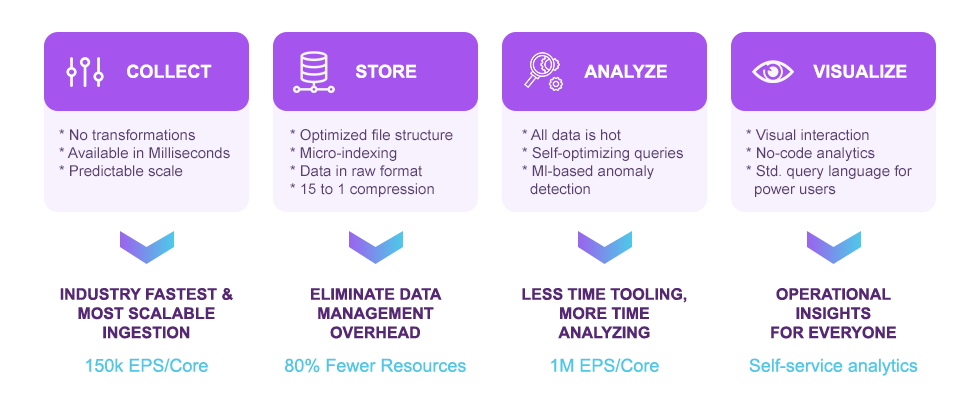
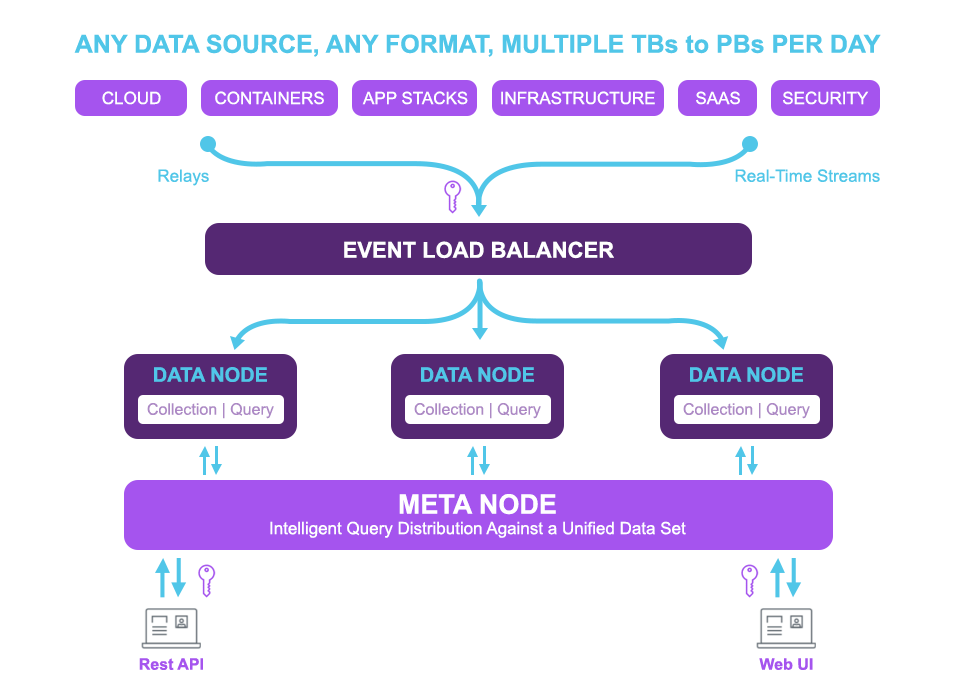
Built With No Compromise Architecture
Helping the world’s most instrumented enterprises unlock the full value of their machine data to move the business forward
- One License, Predictable Cost, Less Expensive
- True real-time queries
- Query at Petabyte scale
- No latency on ingestion
- Point-and-click query builder, no need to learn LINQ
- Cloud-native platform, scale from GB-TB-PB
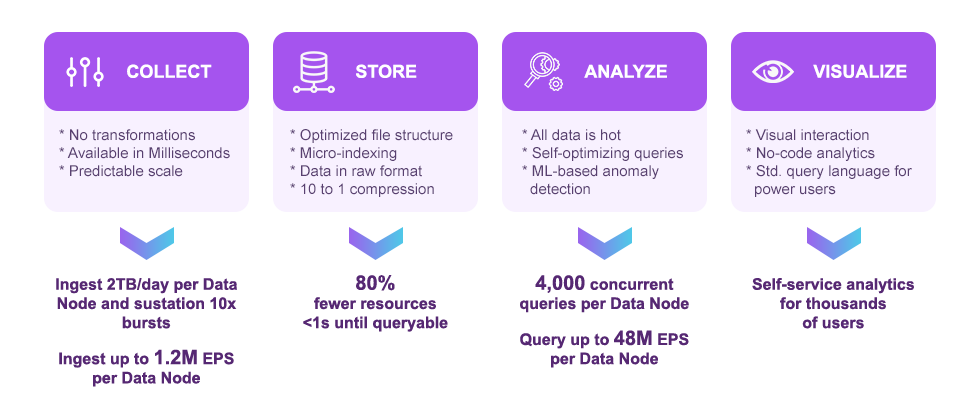
- One data node is able to ingest 2TB/day
- 400 day of hot data by default
- Micro-indexes require only 2% of space
- Easy-to-build dashboards
- Easy to add new sources
- More efficient architecture, lower infrastructure
- Maintenance costs due to reduced footprint
- Storage costs
Built On A No-Compromise Architecture
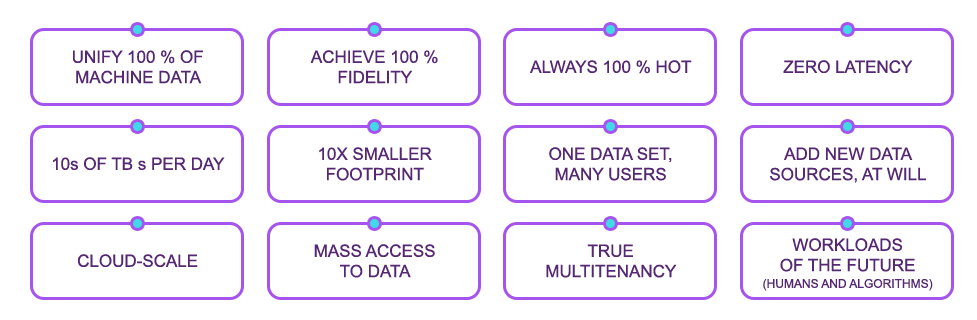
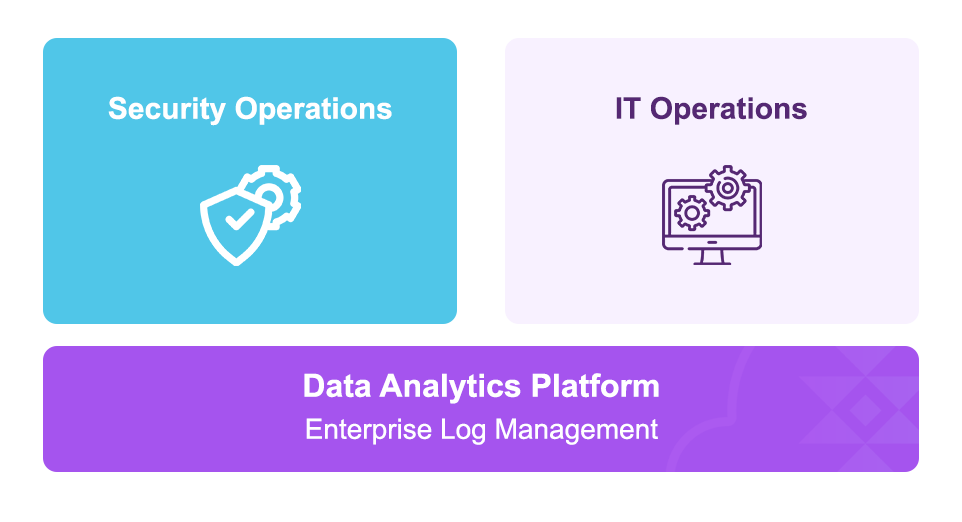
Multiple Use Cases, One Platform, All The Data
Turning machine data into operational value at scale
All Together We Deliver Differentiated Performance, Scale, And Tco
Security Capabilities
Data at Rest Encryption
- Encrypted on Disk with LUKS AES-256
- Managed by the device (Linux OS)
- Customer manages encryption keys
- Independent from storage technology (NVMe, SSD, etc)
Other Key Capabilities
- All activities (queries, views, writes, etc.) for all users are recorded and auditable
- Access is secured by two-factor authentication and HTTPS
- Data sent to the platform can be secured via SSL/TLS with X.509v3 certs
- External queries made with the REST API are secured with HTTPS and X.509v3 certs
See The Past And The Present
All data in our platform is hot, to seamlessly analyze real-time data streams and years of historical data. Micro-indexing technology and compression means Petabytes of data can be queried in a flash, while keeping storage to a minimum.
One Data Set, Many Uses
Multiply the value of the data and enable many downstream teams (IT Ops, SecOps) with a single data set. With our platform, users can easily tailor data access and masking based on user type.
Service Operations
Our Service Operations provides contextual full-stack visibility across an organization’s IT operations at massive speed and scale.
See Other Threats

Collect, analyze, and manage all security and machine data across the enterprise.

Implement analytics, alerts, threat hunting, and forensic analysis

Integrate MI and data science tools
Copyright © 2022. All rights reserved to LOOPCLOUD